Supported Languages
Contrast Security integrates with your tools at every stage of the development lifecycle, making connectivity seamless and fast.
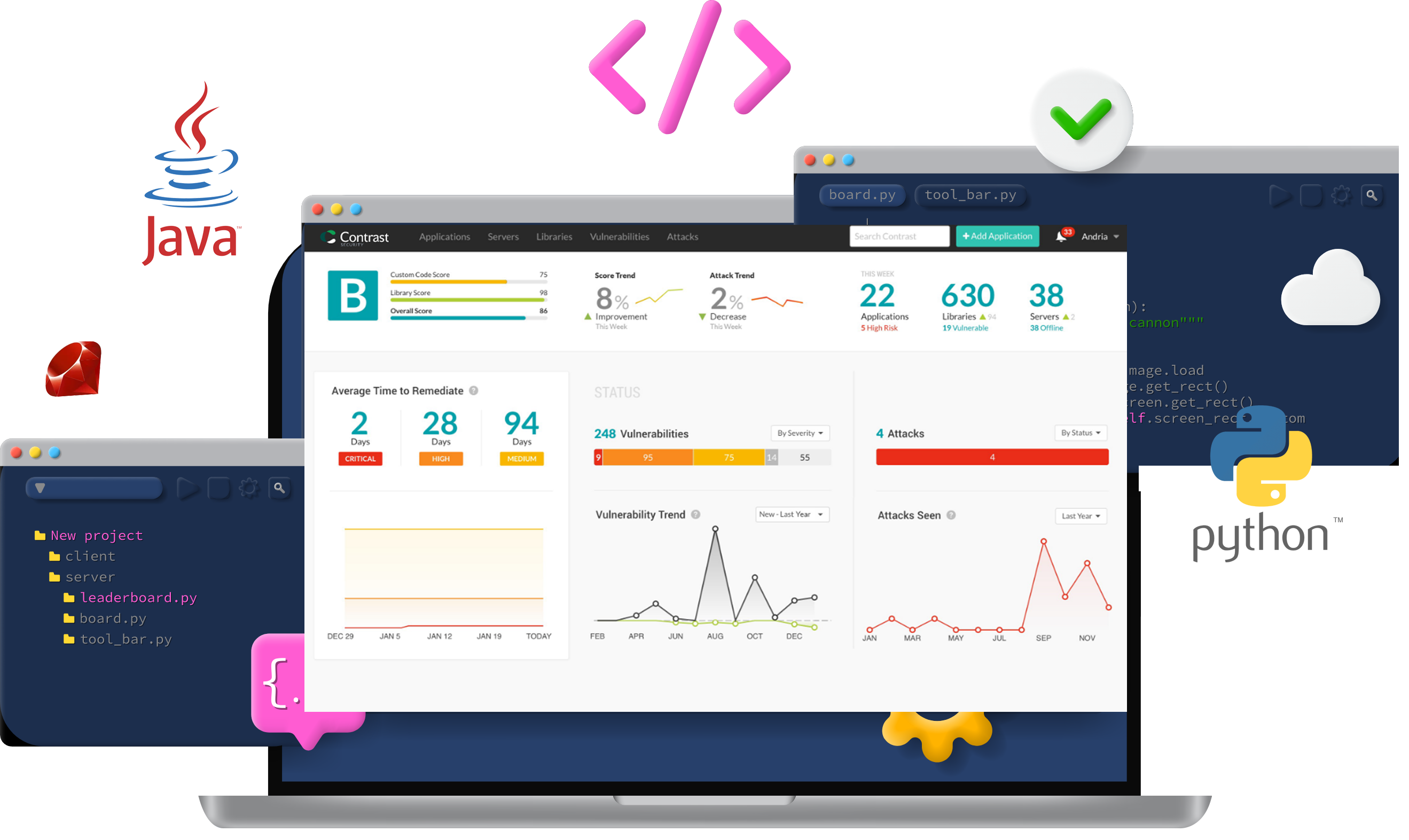
Contrast Security Supported Platforms
Resources to help you get secure code moving
- Show All
- Java
- JavaScript
- .NET
- .NET Core
- NODE.JS
- Ruby
- Python
- GoLang
- Scala
- PHP
- Kotlin

blog: Drupal security challenges faced by developers

blog: Contrast Scan adds support for client-side JavaScript including Angular, React, & jQuery
.NET Core Framewor

blog: Configure a Python agent with Contrast in five minutes

blog: Debunking IAST myths

blog: Debunking IAST myths

blog: Debunking IAST myths
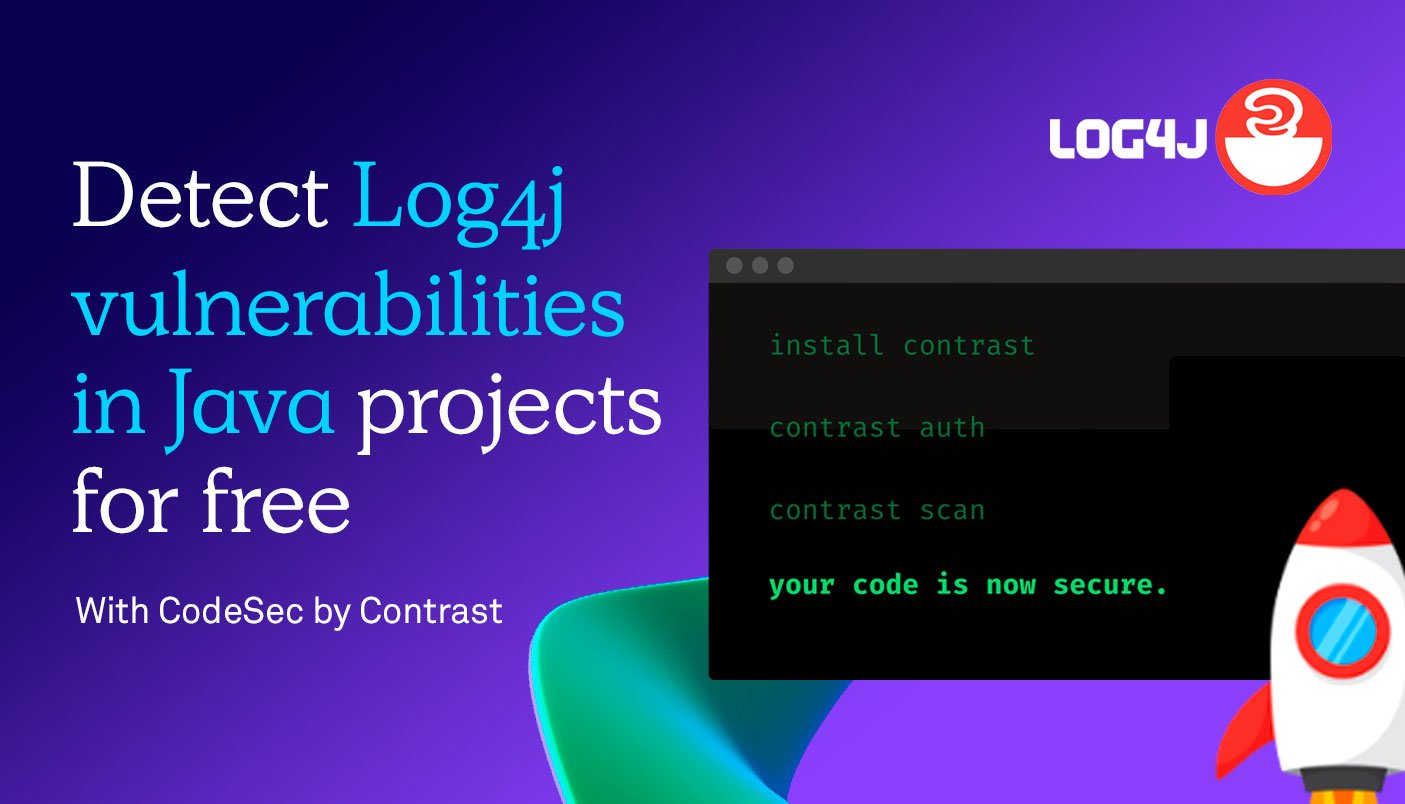
blog: How to detect Log4j vulnerabilities in Java projects for free with CodeSec

blog: Why do modern companies choose Kotlin for server-side development?
blog: Open-Source Python Salt CVEs and the Cisco Server Breach

blog: Secure your PHP Applications with Contrast Security

blog: Securing Server-Side Kotlin

blog: Scaling to Scala

blog: Automating .Net 6 Application Protection

Blog: Understanding Software Supply Chain Risks and How to Mitigate Them

blog: Why Developers Should Care About Our New Go Agent: A Look Under the Hood

blog: Why Developers Should Care About Our New Go Agent: A Look Under the Hood

blog: Contrast Security Further Expands Industry’s Broadest IAST Language Support with the Addition of Python
blog: Using Contrast to Prevent Bootstrap-sass RubyGem Remote Code Execution (RCE)

blog: The Agony and the Ecstasy of Securing .NET Applications

What is Node.js?

Ruby Programming Language
Go Language
What is a MAN-IN-THE-MIDDLE (MITM) ATTACK?
HOW TO INSTRUMENT AN APPLICATION USING RUBY agent
Python Programming Language
Contrast Security Adds Go Language Support For Industry's First Interactive Application Security Analyzer
Contrast Security Announces New Approach to Securing PHP Applications

“HOW TO” INSTRUMENT A NODE agent
![]()
Secure code & serverless environments for free! Through simple command line interface.
![]()
Secure code & serverless environments for free! Through simple command line interface.
Event and Live Demo Announcement

API WORLD
October 25 - November 3rd - LIVE in-person and Virtual
Hear from our very own Steve Wilson, Chief Product Officer, at API World where thousands of global technical leaders, engineers, software architects, and executives at the world’s largest and longest-running API & microservices event – in its 11th year!

OWASP GLOBAL APPSEC
November 14–18, 2022 | San Francisco, CA
Designed for private and public sector infosec professionals, the two day OWASP conferences equip developers, defenders, and advocates to build a more secure web.

live Webinar: THREATS FACING THE FINANCIAL SECTOR: FROM HEIST TO HOSTAGE SITUATION
November 3rd, 2022 | 10am PT / 1pm ET
Financial institutions face evolving cybercrime conspiracies coordinated by international cyber cartels.
















